The average SOC receives nearly 4,000 alerts per day. Two-thirds are never investigated. When speed determines whether a breach is contained or catastrophic, the architecture of your triage process is not a preference, it is a strategic decision.
By Miro Pihkanen, CSO

In an emergency department, no one expects surgeons to assess every patient who walks through the door. A triage nurse evaluates, prioritises, and routes so that specialists focus on the cases that demand their expertise. The modern SOC faces the same challenge, at a scale no human team can manage alone. When a genuine threat hides among thousands of false positives, the question of who, or what, makes the first triage call is the difference between containment and catastrophe.
The Triage Crisis: Volume, Speed, and a Vanishing Workforce
Security Operations Centres are under siege, not from attackers, but from their own detection systems. The average SOC receives 3,832 alerts per day, and 67% are never investigated. This is not negligence. It is maths. There are simply too many signals for human analysts to process. Understanding is the first step toward solving this.Understanding what SIEM can and cannot do is the first step toward solving this.
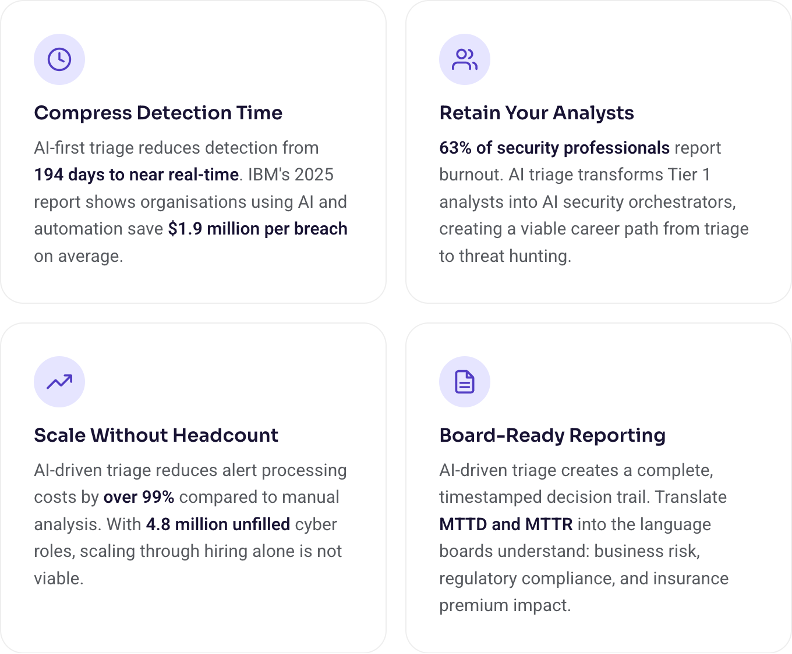
The consequences are measurable and severe. IBM reports that the average breach takes 194 days to identify and a further 64 days to contain, a total lifecycle of 258 days during which attackers move laterally, escalate privileges, and extract data. The average cost? $4.88 million per breach, up 10% year-over-year. IBM Cost of a Data Breach Report, 2024
This is compounded by a structural workforce crisis. ISC2’s 2024 Cybersecurity Workforce Study found a global gap of 4.8 million cybersecurity professionals, a 19% increase from the prior year. 90% of organisations report skills shortages. The problem cannot be solved by hiring alone. ISC2, 2024
The economics tell the story plainly. Industry research shows that AI-driven triage can reduce alert processing costs by over 99% compared to manual analysis. At nearly 4,000 alerts per day, the difference is not marginal, it is structural. IBM’s 2025 report found that organisations using AI and automation in their security workflows saved an average of $1.9 million per breach. IBM, 2025
The answer must be architectural, not incremental.
Five Approaches to SOC Triage, and Where Each Falls Short
1. Human Analyst, Every Time
The traditional model. Every alert receives human eyes. An analyst reviews context, makes a judgment call, escalates or closes. This delivers the highest quality per decision, but it does not scale. When 67% of alerts go untouched, the model has already failed. Not because analysts are careless, but because alert volumes have outpaced human cognitive bandwidth.
The human cost is equally unsustainable: 63% of security professionals report burnout, and 55% have considered leaving their roles entirely. Average analyst tenure sits at just 1-3 years. Tines, 2023; Dark Reading, 2024
2. Automated Playbooks: Predefined Steps
SOAR platforms execute predefined response sequences: if alert matches pattern X, run steps A, B, C. Playbooks handle known scenarios efficiently and reduce manual workload for common alert types. They are valuable for operational hygiene, but they are inherently reactive. They can only respond to what has been anticipated.
Novel attack patterns, zero-day exploits, and sophisticated multi-stage intrusions fall outside any predefined playbook. When adversaries innovate faster than rules can be written, playbooks become a floor, not a ceiling.
3. AI First, Human on Escalation
AI processes the full alert stream in real time, filtering noise, correlating signals across data sources, and surfacing only the events that warrant human attention. Analysts focus their expertise on complex investigations, threat hunting, and strategic decisions rather than drowning in routine triage.
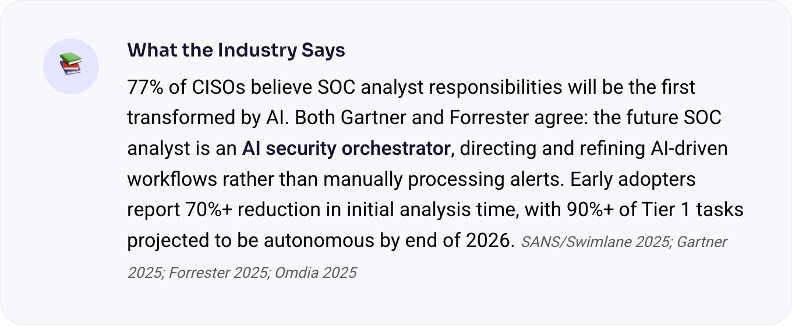
Both Gartner and Forrester converge on this point. Gartner’s 2025 research identifies AI SOC agents as most promising for triage, enrichment, and reporting, the high-volume, pattern-matching tasks that consume analyst hours. Forrester’s position is equally clear: the fully autonomous SOC remains unrealistic; the future is analysts as AI security orchestrators. Gartner Predict 2025; Forrester, 2025
4. Threat-Level Dependent Routing
A pragmatic variation: the triage method adapts based on assessed severity. Low-severity alerts are auto-resolved, medium-severity alerts follow playbooks, and high-severity alerts go directly to senior analysts. The challenge is that accurate severity scoring itself requires intelligent analysis, which brings you back to the need for AI at the front of the pipeline.
5. Fully Autonomous AI Response
At the frontier: AI systems that not only triage but also respond autonomously, isolating endpoints, blocking IPs, revoking credentials without waiting for human approval. Speed is maximised, but so is risk. The maturity of the AI, the quality of its training data, and the governance framework around it determine whether autonomous response is a force multiplier or an operational liability.
The Evidence: Where AI Triage Is Already Working
This is not theory. Organisations across sectors are already deploying AI-first triage with measurable results:
- A leading global IT services provider deployed an AI-enabled SOC with SOAR integration and reported a 60% reduction in alert fatigue alongside 50% faster incident response times.
- A major platform vendor’s phishing triage agent (launched 2025) autonomously classifies phishing alerts, detecting 6.5x more confirmed malicious alerts with a 77% improvement in verdict accuracy compared to manual review.
- Big Four consulting firms are now partnering with security vendors to build enterprise-grade agentic SOC services, validating the category at the highest levels of enterprise adoption.
The cautionary example is equally instructive. The Change Healthcare ransomware attack resulted in projected costs exceeding $2.3 billion for UnitedHealth Group, a stark illustration of what happens when triage fails and a threat moves through the kill chain undetected. UnitedHealth Group SEC Filing, 2024

How AI-First Triage Works in Practice
Understanding the mechanics matters. AI-first triage is not a black box. It is a structured pipeline that augments human capability at every stage.
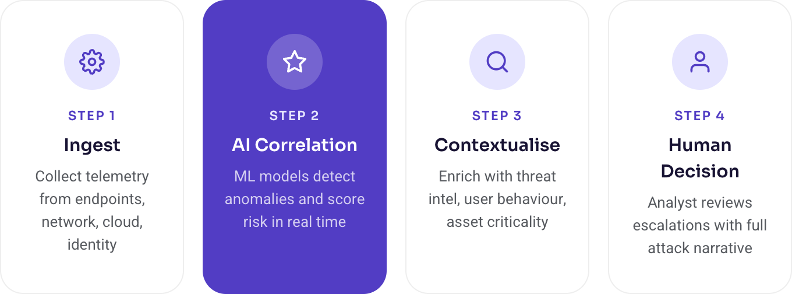
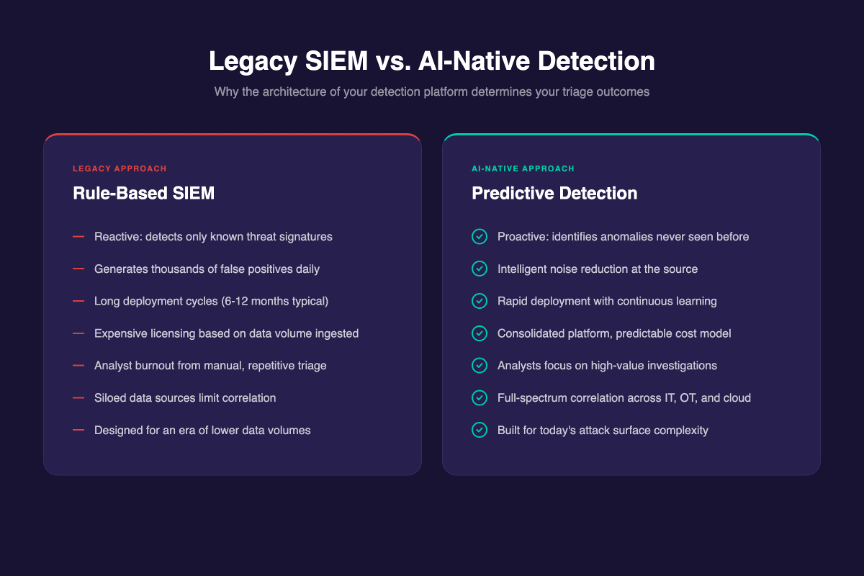
The critical difference is what happens at Step 2. Legacy systems match against static rules; they can only find what they have been told to look for. AI-native platforms learn what is normal for your environment and surface what is not, including threats that have never been catalogued. This is the shift from reactive monitoring to predictive detection, and it represents .
This is the shift from reactive monitoring to predictive detection, and it represents the future of SIEM.
The Rise of the Agentic SOC, and Why Governance Matters
The industry is moving rapidly from “AI-assisted” security to what is now being called the Agentic SOC, autonomous AI agents that can plan, investigate, decide, and act on security events without waiting for human instruction. Every major platform vendor launched autonomous triage agents in 2025. Omdia projects the Agentic SOC will become the standard operating model within 1-2 years.
But capability without governance is a liability. IBM found that 63% of organisations lack formal AI governance policies for their security operations. VentureBeat reports that 40% of SOC automation projects fail not because the technology underperforms, but because organisations deploy without adequate boundaries, oversight, or accountability frameworks.
The organisations getting this right share a common principle: bounded autonomy. AI agents operate within expert-defined guardrails. Every decision is inspectable. Every escalation is documented. Human oversight is not a bottleneck, it is the governance layer that makes autonomous speed safe. This is not a trade-off between speed and control. It is an architecture that delivers both.
What This Means for Security Leaders
For CISOs and security directors, the triage architecture you choose has implications far beyond the SOC floor. Here is what the data shows:
The Blacklight Approach
At Blacklight, we built our platform around a fundamental conviction: the first triage decision should be made by AI, every time, at machine speed, with full contextual awareness. Not as a replacement for human expertise, but as a force multiplier for it.
Why Blacklight Is Different
Most legacy SIEM and detection platforms were built in an era when data volumes and adversary speed were a fraction of what they are today. They rely on predefined rules and known attack signatures, generating thousands of false positives while missing novel threats entirely. Bolt-on AI features added to legacy architectures inherit these limitations.
Blacklight was built with AI at the core from day one, not retrofitted. Our AI-powered monitoring and detection platform processes the full alert stream in real time, correlating signals across endpoints, network traffic, cloud workloads, identity systems, and operational technology. It does not look for what it expects to find. It learns what is normal for your environment and identifies what is not, including threats that have never been seen before. This is predictive detection, not reactive monitoring.
Human analysts receive high-confidence, contextually enriched escalations, not raw alerts. They see the full attack narrative, not isolated data points. Every AI decision is inspectable, every action auditable, every escalation governed by expert-defined boundaries. This is what it means to have a command centre for your organisation, delivering speed where it counts, clarity where it matters, and governance built in from the ground up.
Deployed as SaaS or fully managed SOC-as-a-Service , Blacklight covers the full security lifecycle, from proactive monitoring and AI-powered detection to automated response and strategic threat hunting, on a single unified platform across IT, OT, and blockchain infrastructure with full visibility from Day 1.